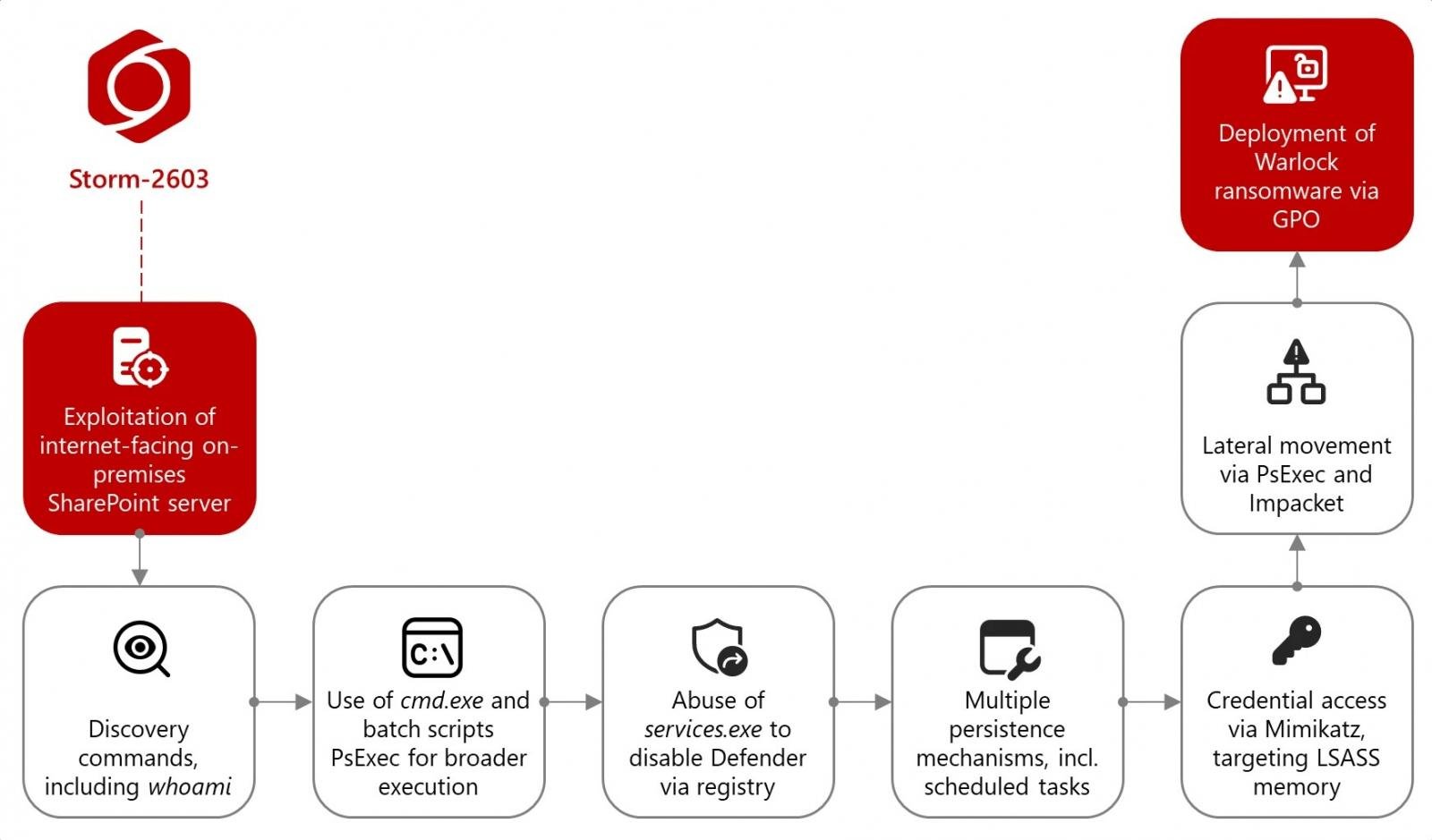
A Chinese hacking group is deploying Warlock ransomware on Microsoft SharePoint servers vulnerable to widespread attacks targeting the recently patched ToolShell zero-day exploit chain.
Tracked as Storm-2603, these China-based threat actors were also previously linked by Microsoft researchers to Lockbit ransomware attacks.
“Microsoft tracks this threat actor in association with attempts to steal MachineKeys using the on-premises SharePoint vulnerabilities,” the company said in a Wednesday report. “Starting on July 18, 2025, Microsoft has observed Storm-2603 deploying ransomware using these vulnerabilities.”
After breaching the victims’ networks, Storm-2603 operators use the Mimikatz hacking tool to extract plaintext credentials from LSASS memory.
They then move laterally with PsExec and the Impacket toolkit, executing commands via Windows Management Instrumentation (WMI), and modifying Group Policy Objects (GPOs) to deliver Warlock ransomware across compromised systems.
“The group that Microsoft tracks as Storm-2603 is assessed with moderate confidence to be a China-based threat actor. Microsoft has not identified links between Storm-2603 and other known Chinese threat actors,” the company added.
“Customers should apply the on-premises SharePoint Server security updates immediately and follow the detailed mitigation guidance in our blog,” Microsoft warned.
Microsoft Threat Intelligence researchers have also linked the Linen Typhoon and Violet Typhoon Chinese state-backed hacking groups with these attacks on Tuesday, days after Dutch cybersecurity firm Eye Security first detected zero-day attacks exploiting the CVE-2025-49706 and CVE-2025-49704 vulnerabilities.
Since then, Eye Security CTO Piet Kerkhofs told BleepingComputer that the number of breached entities is much larger, with “most of them already compromised for some time already.” According to the cybersecurity company’s statistics, the attackers have so far infected at least 400 servers with malware and breached 148 organizations worldwide.
CISA also added the CVE-2025-53770 remote code execution flaw, part of the same ToolShell exploit chain, to its catalog of vulnerabilities exploited in the wild, ordering US federal agencies to secure their systems within a day.
However, earlier this week, the Department of Energy confirmed that the National Nuclear Security Administration’s networks were breached in the ongoing Microsoft SharePoint attacks, although the agency has yet to find evidence that sensitive or classified information was compromised in the incident.
According to a Bloomberg report, the attackers have also hacked into systems at the US Department of Education, the Rhode Island General Assembly, and Florida’s Department of Revenue, as well as networks of national governments in Europe and the Middle East.
