Microsoft has seized 240 domains used by customers of ONNX, a phishing-as-a-service (PhaaS) platform, to target companies and individuals across the United States and worldwide since at least 2017.
According to Microsoft’s Digital Defense Report 2024, ONNX (also known as Caffeine and FUHRER) was the top Adversary in the Middle (AitM) phishing service by volume of phishing messages during the first half of 2024. Tens to hundreds of millions of phishing emails targeted Microsoft 365 accounts each month and customers of various other tech companies.
“These ‘do it yourself’ kits make up a significant portion of the tens to hundreds of millions of phishing messages observed by Microsoft each month and the fraudulent ONNX operation was a top 5 supplier in the first half of 2024,” Microsoft told BleepingComputer.
“The fraudulent ONNX operation offered phishing kits designed to target a variety of companies across the technology sector, including Google, DropBox, Rackspace, and Microsoft.”
ONNX promoted and sold the phish kits on Telegram using several subscription models (Basic, Professional, and Enterprise), ranging from $150 to $550 monthly.
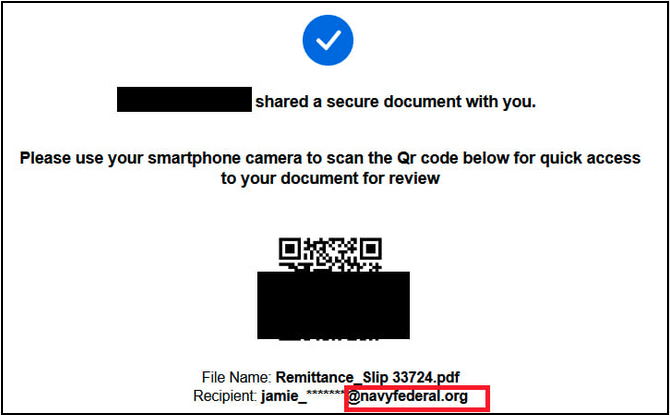
The attacks, also controlled via Telegram bots, came with built-in two-factor authentication (2FA) bypass mechanisms and most recently targeted financial firms’ employees (at banks, credit union service providers, and private funding firms) using QR code phishing (also known as quashing) tactics.
These emails included PDF attachments containing malicious QR codes that redirected potential victims to pages resembling legitimate Microsoft 365 login pages and asked them to enter their credentials.
“Threat actors leverage quishing attacks because victims will typically scan QR codes on their personal mobile devices (which the victim may use for business purposes, as part of their firms’ Bring Your Own Device (BYOD) program),” U.S. securities industry regulator FINRA also warned in a recent alert. “As a result, these attacks are exceptionally difficult to monitor with typical endpoint detection.”
Cybercriminals using ONNX have been particularly effective in carrying out their attacks as the phishing kits help bypass two-factor authentication (2FA) by intercepting 2FA requests. They also use bulletproof hosting services that delay phishing domains’ takedowns and encrypted JavaScript code that decrypts itself during page load, adding an extra layer of obfuscation to evade detection by anti-phishing scanners.
“These attacks present a unique challenge for cybersecurity providers as they appear as an unreadable image to security and scanning features,” said Steven Masada, Assistant General Counsel at Microsoft’s Digital Crimes Unit, today.
ONNX operations abruptly stopped in June after Dark Atlas security researchers discovered and disclosed its owner’s identity, Abanoub Nady (also known online as MRxC0DER).
“Through a civil court order unsealed today in the Eastern District of Virginia, this action redirects the malicious technical infrastructure to Microsoft, severing access of threat actors, including the fraudulent ONNX operation and its cybercrime customers, and permanently stopping the use of these domains in phishing attacks in the future,” Masada added.
“Our goal in all cases is to protect customers by severing malicious actors from the infrastructure required to operate and to deter future cybercriminal behavior by significantly raising the barriers of entry and the cost of doing business. We are joined by co-plaintiff LF (Linux Foundation) Projects, LLC, the trademark owner of the actual registered ‘ONNX’ name and logo.”
You can find the complete list of 240 domains seized in the action in the unsealed complaint appendixes.
In October, Microsoft and the Justice Department also disrupted Russian ColdRiver FSB hackers’ attack infrastructure by seizing over 100 domains used in spear-phishing attacks against U.S. government employees and Russian nonprofit organizations.
Last December, the company’s Digital Crimes Unit also took action against a major cybercrime-as-a-service provider (Storm-1152) that registered over 750 million fraudulent Microsoft email accounts and raked in millions by selling them to other cybercriminals.